SOC 2 is an auditing procedure for service providers that's designed to evaluate data-management measures across five trust service principles. These include security, availability, processing integrity, confidentiality, and privacy. A SOC 2 audit will report on the operational effectiveness of these areas, and successfully passing the audit can be a gateway to business growth.
While most business leaders appreciate the importance of backup, robust backup and disaster recovery strategies are sorely lacking in many organizations. Fortunately, by working closely with a disaster recovery specialist and investing in managed disaster recovery services, you can help to reduce risk and achieve compliance.
SOC 2 and Backup & Disaster Recovery
You may be wondering if SOC 2 actually requires backup and disaster recovery.
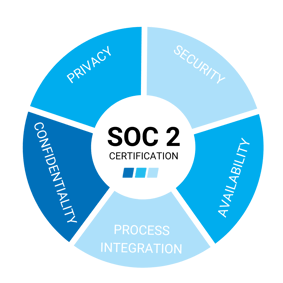 SOC 2 explicitly requires organizations to maintain up-to-date backups of client data in remote locations. It also stipulates that a business continuity plan is created and that all procedures are thoroughly tested. While compliance allows for a significant degree of flexibility, backup and disaster recovery in SOC 2 broadly falls under the trust services criteria of availability. Not only must data be kept secure from threats like exfiltration or malware infection – but it also needs to be readily available.
SOC 2 explicitly requires organizations to maintain up-to-date backups of client data in remote locations. It also stipulates that a business continuity plan is created and that all procedures are thoroughly tested. While compliance allows for a significant degree of flexibility, backup and disaster recovery in SOC 2 broadly falls under the trust services criteria of availability. Not only must data be kept secure from threats like exfiltration or malware infection – but it also needs to be readily available.
Backup and disaster recovery are addressed under the Additional Criteria for Availability. The section A1.2 states the requirement for documented data backup and recovery processes and infrastructure, while Section A1.3 states that these recovery plans and procedures must be tested on a regular basis to ensure they meet their objectives.
By enlisting the help of a disaster recovery specialist, you’ll be better positioned to follow industry-standard best practices. This involves creating a comprehensive disaster recovery plan that details the processes of how you'll respond to issues such as hardware failures or loss of cloud services. It also involves setting your recovery goals – specifically recovery point objectives (RPOs) and recovery time objectives (RTOs). These parameters, which are usually system-specific, define how much data you can afford to lose and the maximum amount of time it should take to get affected systems back up and running.
Ensure Your Records Are Always Available
SOC 2 demand requires that organizations have certain controls in place to ensure the availability of critical services and data. Naturally, this means a strong backup and disaster recovery is a key part of ensuring high availability. Clients should always have access to their services and data, for both the sake of compliance and customer satisfaction.
While your Service Level Agreements (SLAs might allow for some degree of scheduled downtime, backup and disaster recovery keeps unscheduled downtime to a minimum and helps you meet the obligations of your SLAs. If your records are always available thanks to automated backup processes, rollovers, and redundant systems, you’ll be a step closer to achieving compliance with the availability requirements of SOC 2.
Protect Your Records From Cyberthreats
Client data must be protected throughout its entire lifecycle. Backup and disaster recovery is an essential fallback in the event that mission-critical systems are attacked by ransomware or any other threat that could destroy data or render it inaccessible. It’s important that your backup and disaster recovery solution also offers security measures of its own, including full endpoint and end-to-end encryption.

To pass a SOC 2 audit, you will need remotely hosted backups. One common strategy to follow is the 3-2-1 approach to backup, which includes three copies of the data on two different types of media with one stored off-site.
However, your disaster recovery specialist may recommend the 3-2-2 or the 3-2-3 strategy, which accounts for two or three remote backups respectively.
Respond Quickly to Data Loss Incidents
While most of us understand the importance of backing our data up, actual recovery processes often end up being overlooked. Without incorporating recovery into your business continuity plan, your backups may not be readily accessible, thus leading to significant disruption to your business. This, in turn, may result in a failure to meet the availability requirements mandated by SOC 2 compliance.
It’s imperative that businesses can respond quickly to data loss incidents according to their recovery time objectives. With automated rollovers and redundant systems hosted online, it’s possible to keep unscheduled downtime to a minimum and, in many cases, eliminate it fully. That said, there still needs to be a documented set of procedures outlining what needs to be done following a data loss incident.
Take Advantage of New Backup Options
In the old days, companies typically backed up their data locally on storage networks and used tape drives to create portable backups, which were then shipped off to a remote location. This approach is rather cumbersome and should not be what you're relying on, today. To meet the accessibility requirements of SOC 2, businesses should take advantage of modern backup systems such as managed disaster recovery services.
Cloud computing offers the obvious solution. Cloud data centers have multiple redundancies and, because they exist outside your network and have their own security controls, they aren't subject to the same vulnerabilities. This adds crucial extra layers of protection that will help ensure your data is always available and that you’re ready to pass your SOC 2 audit with flying colors.
Editor's Note: This post was originally published in February 2021 and has been updated for accuracy and comprehensiveness.
Charles IT exhaustively assesses your computing infrastructure to identify any security holes. Call us today to schedule your first consultation.

.png)