
As our world becomes more digitalized, businesses are finding themselves vulnerable to an escalating danger: cyberattacks. Cybercriminals have an array of techniques at their disposal, from malware and ransomware to phishing attacks, all designed to steal sensitive data, disrupt operations, and inflict financial losses. So, what are the solutions? What can organizations do to counteract a cyber attack? Well, there are many available options, many of which cover your bases on different levels and work together to keep your network secure.
In this increasingly hostile environment, it is more important than ever for businesses to have a strong cybersecurity posture. One of the best ways to do this is to implement a managed detection and response (MDR) solution.
MDR is a cybersecurity service that provides businesses with 24/7 monitoring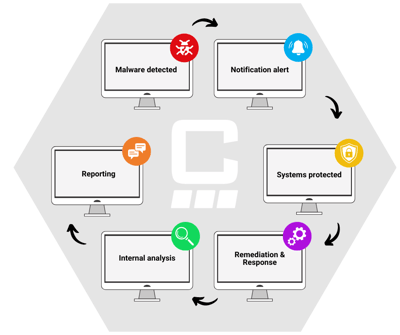 and threat detection and response capabilities. MDR providers use a combination of advanced technologies, human expertise, and threat intelligence to identify and respond to potential security incidents quickly and effectively. This is the absolute best way for organizations to learn of an attack, and swiftly take action. Without MDR, you may not know about an attack until it's too late and the damage is done; in order to have good IT security, you need to be able to recognize these attacks as they are happening, because attackers move quickly.
and threat detection and response capabilities. MDR providers use a combination of advanced technologies, human expertise, and threat intelligence to identify and respond to potential security incidents quickly and effectively. This is the absolute best way for organizations to learn of an attack, and swiftly take action. Without MDR, you may not know about an attack until it's too late and the damage is done; in order to have good IT security, you need to be able to recognize these attacks as they are happening, because attackers move quickly.
Five key benefits of MDR

Early threat detection: MDR providers use a variety of methods to detect threats, including continuous monitoring of network traffic, endpoint devices, and cloud applications. This allows them to identify and respond to threats quickly, before they have a chance to cause damage.
-
- For example, MDR providers can use machine learning to identify patterns of malicious activity that may be missed by traditional security solutions.
- They can also use threat intelligence to identify threats that are known to be targeting businesses in your industry.
Protection against unknown threats: MDR providers use advanced threat intelligence to identify and protect against even the latest and most sophisticated threats. This is important because many cyberattacks use new or unknown malware that traditional security solutions cannot detect.
Rapid incident response: When a threat is detected, MDR providers respond quickly to contain the incident and minimize damage. This can help to reduce the impact of a cyberattack and prevent it from disrupting business operations.
-
- MDR providers have a team of experts who are available 24/7 to investigate and respond to security incidents.
- They can also work with your IT team to implement remediation measures to prevent the threat from spreading.
Reduced cost of security: MDR can help businesses reduce the cost of security by offloading the burden of monitoring and responding to threats to a third-party provider. This can free up IT staff to focus on other tasks, such as improving business processes.
Improved compliance: MDR can help businesses improve their compliance with industry regulations, such as HIPAA and GDPR. This is because MDR providers can help businesses to implement and maintain security controls that meet the requirements of these regulations.
-
- MDR providers have experience in working with businesses to comply with regulations.
- They can also provide guidance and support to help businesses stay compliant.
Key features of MDR solutions
Continuous monitoring of network traffic, endpoint devices, and cloud applications: MDR providers continuously monitor your network, endpoints, and cloud applications for signs of malicious activity. This includes monitoring network traffic, file changes, and user behavior.
applications: MDR providers continuously monitor your network, endpoints, and cloud applications for signs of malicious activity. This includes monitoring network traffic, file changes, and user behavior.
- They use a variety of tools and techniques to do this, including:
- Network traffic analysis
- Endpoint detection and response (EDR)
- Cloud security posture management (CSPM)
- User behavior analytics (UBA)
Advanced threat intelligence: MDR providers use advanced threat intelligence to identify and protect against even the latest and most sophisticated threats. This intelligence is gathered from a variety of sources that keep up to date with the latest happenings in cyber crime.
Rapid incident response: When a threat is detected, MDR providers respond quickly to contain the incident and minimize damage. This includes:
-
- Investigating the incident to determine the extent of the compromise
- Isolating the affected systems
- Removing the threat
- Recovering lost data
24/7 support: MDR providers offer 24/7 support, so you can always get help when you need it. This includes support for incident response, troubleshooting, and training.
Choosing an MDR Provider
If you are considering implementing an MDR solution, there are a few factors you should keep in mind when choosing a provider.
-
The provider's experience and expertise: Make sure the provider has experience in detecting and responding to a variety of cyberattacks.
- Ask the provider about their experience with different types of threats, such as ransomware, phishing, and data breaches.
- You can also check the provider's website for case studies or testimonials from other customers.
-
The capabilities of the provider's platform: The provider's platform should be able to monitor your environment effectively and respond to incidents quickly.
- Ask the provider about the features and capabilities of their platform.
- You should also ask about the provider's track record of detecting and responding to incidents.
-
The level of support offered by the provider: Make sure the provider offers 24/7 support so you can always get help when you need it.
- Ask the provider about their support hours and how they will contact you in the event of an incident.
- You should also ask about the provider's training and documentation resources.
-
The cost of the solution: The cost of MDR solutions varies depending on the features and functionality offered.
- Get quotes from several providers to compare prices.
- You should also factor in the cost of any additional services, such as training or incident response.
Additional considerations when choosing an MDR provider
- The provider's security certifications: Make sure the provider has the necessary security certifications, such as SOC 2 and ISO 27001.
- The provider's customer references: Ask the provider for customer references so you can speak to other businesses that have used the provider's services.
- The provider's pricing model: Make sure you understand the provider's pricing model before you sign a contract.
By carefully considering these factors, you can choose an MDR provider that can help you protect your business from cyberattacks.
MDR is a valuable tool that can help businesses of all sizes protect themselves from cyberattacks. By providing continuous monitoring, advanced threat intelligence, and rapid response to incidents, MDR can help businesses to reduce their risk of a cyberattack and minimize the impact of an attack if it does occur. In today's threat landscape, MDR is an essential security solution for businesses of all sizes.
If you're looking for assistance in any capacity with managed detection and response, Charles IT's experienced team can help! We specialize in all things IT and cybersecurity related, and would be happy to provide our expertise in educated your organization, as well as implementing any solutions you may need. Reach out to us today to get the ball rolling on managed detection and response solutions!




