
SEC cybersecurity guidelines aren’t there for the fun of it. Instead, they are in place to safeguard your business and consumers from monetary losses.
What happens if your business is the target of a data hack that releases yours or your customer’s sensitive information? First, you would most likely be on the hook for fines and penalties from regulatory agencies. Second, your business could have a tarnished brand image for years to come.
Avoiding the financial and non-financial impacts of cybersecurity threats can be done by prioritizing controls in user security and access, disaster recovery and response, and vulnerability management.
#1: User Security and Access
The first set of SEC cybersecurity guidelines that your business can’t afford to ignore is user security and access. This section of guidelines helps prevent data theft by someone who has physical access to your network devices. 
This could be an employee or an independent contractor with network access. Without the proper controls in place, your business could face a significant financial loss from fraud or asset misappropriation.
Take the recent Equifax data breach settlement. In 2017, Equifax experienced a data breach that released the information of more than 147 million customers, resulting in a $425 million settlement. This is a significant financial loss, which is why it’s important that your business focuses on internal controls.
#2: Disaster Recovery and Response
The next component of SEC cybersecurity guidelines that you should comply with is disaster recovery and response. This control makes sure your business can continue running smoothly in the event of a disaster, such as a robbery or financial crisis.
With the proper controls in place, your business can thwart claims of negligence, ensure financial reporting regulatory requirements are upheld, and guarantee everyone on your team is ready to act when disaster does strike.
For example, Hurricane Sandy caused significant and wide-ranging damage throughout the northeast coast on October 28th and 29th, 2012. Many businesses weren’t prepared for this disaster, causing business operations to halt altogether. This led to negative impacts on an estimated 60,000 to 100,000 small businesses.
#3: Vulnerability Management
The third SEC cybersecurity guideline that financial firms can’t afford to ignore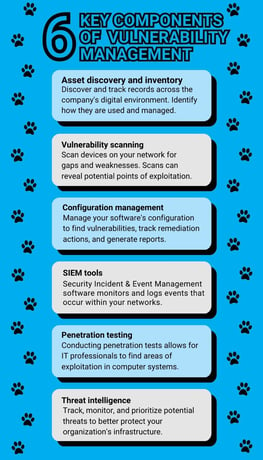 is vulnerability management. How easily can bad actors get into your network and access confidential information? If you’re not sure, odds are you may need to revamp your security features.
is vulnerability management. How easily can bad actors get into your network and access confidential information? If you’re not sure, odds are you may need to revamp your security features.
The average cost of a data breach in the financial sector is $5.72 million. Would this bankrupt your business? Both insider and outsider threats are increasing, causing investors to want added transparency in operations.
Take the recent fraud uncovered in FTX, an up-and-coming crypto trading platform. Bankman-Fried, a majority owner, was found embezzling funds to invest in a personal hedge fund, buy homes in the Bahamas, and donate to political campaigns. Bankman-Fried was arrested with a new CEO stepping in. This is just one example of poor vulnerability management controls in a financial business.
Summary
Is your business properly following SEC cybersecurity requirements? If not, now is the perfect time to reevaluate your existing procedures to safeguard the sensitive information of your business and prevent a bankrupting monetary loss.
For more information on where your business may be falling short, schedule a meeting today.

.png)


