
Is your business expanding? Maybe you’re entering new markets, offering more products, or adapting to changing remote workforce demands. Finally seeing your revenue increase or your profitability skyrocket can be great, but these newfound changes can come with added cybersecurity risks for your organization.
When it comes to the IT security of your business, endpoint encryption can safeguard your sensitive information from both internal and external threats. So, what is encryption in cyber security and what are the ways that endpoint encryption can protect your business?
What is Encryption in Cyber Security?
Cybersecurity encryption is one way to safeguard sensitive information in your business. This can involve a variety of strategies, such as full disk encryption, folder encryption, and transparent file encryption. Full disk encryption protects your information at the hardware level by encrypting all information found on the disk drive and is one of the most comprehensive encryption options for businesses.
business. This can involve a variety of strategies, such as full disk encryption, folder encryption, and transparent file encryption. Full disk encryption protects your information at the hardware level by encrypting all information found on the disk drive and is one of the most comprehensive encryption options for businesses.
What are Ways Endpoint Encryption Safeguards Your Business?
Endpoint encryption secures the endpoints in your business, which could be employee laptops or business phones. Hackers will often target your business’s endpoints because they are more likely to be vulnerable and lack the necessary controls. The right endpoint encryption IT security features can provide the following safeguards:
#1: Minimizes Risks Associated with Lost Devices
If your employee travels for work and accidentally leaves their laptop at the airport, are you confident everything is secured? If someone were to pick up their laptop, could they gain access to your customer list or bank account information? Endpoint encryption secures the device, preventing unauthorized access to critical information.
#2: Limits the Transfer of Confidential Information
Every business has confidential information, from customer credit cards and personal information to business bank accounts and employee payroll details. Hackers that gain access to this information may try and exploit your business and request ransom or leak the information, both of which hurt your brand image and financial health. Endpoint encryption limits the transfer of confidential information to unauthorized parties, giving your business added security.
personal information to business bank accounts and employee payroll details. Hackers that gain access to this information may try and exploit your business and request ransom or leak the information, both of which hurt your brand image and financial health. Endpoint encryption limits the transfer of confidential information to unauthorized parties, giving your business added security.
#3: Secures Communication Channels
As a business, you most likely exchange information on a daily basis. Without the right endpoint encryption solutions worked into your network, you risk sending information through unsecured channels. This makes your business more susceptible to attacks. By ensuring your endpoints are secure, your information can be transmitted securely and safely.
#4: Reduces Vulnerability in the Internet of Things
The Internet of Things (IoT) is a term used to describe various pieces of technology working together under a single network. This could be anything from software programs to individual devices. Despite providing your business with the ability to enjoy higher productivity, the IoT does present additional vulnerabilities. Endpoint encryption can minimize threats associated with the connectivity of your business. Simply put, if one piece of technology is compromised, and it’s encrypted, it won’t affect the rest of your network.
#5: Lowers Losses Associated with Poor Training
Most data breaches occur from within your company. In fact, in 2022 over 80%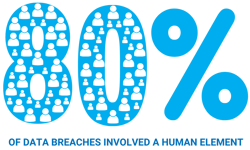 of data breaches involved a human element from an employee clicking on a phishing email or unknowingly sending information to a fraudulent person. Implementing endpoint encryption can improve employee monitoring controls and limit the information being transmitted from endpoints.
of data breaches involved a human element from an employee clicking on a phishing email or unknowingly sending information to a fraudulent person. Implementing endpoint encryption can improve employee monitoring controls and limit the information being transmitted from endpoints.
Summary
When it comes to the IT security controls in your business, you don’t want to cut corners. This not only increases your risk of becoming a target for a data breach but can also lead to financial losses for your organization.
To understand how your organization can leverage endpoint encryption to minimize risks and maximize security, reach out to Schedule a Call today!




