
In today's digital landscape, where cyber threats are constantly evolving, vulnerability scanning has become more crucial than ever for organizations. It serves as a proactive measure to identify and mitigate potential vulnerabilities that could be exploited by cybercriminals. By conducting regular vulnerability scans, businesses can significantly reduce their risk of a data breach and protect their sensitive information.
Vulnerability scanning plays a vital role in an organization's IT security compliance program. It helps to ensure that businesses meet regulatory requirements imposed by industry standards and government regulations such as PCI DSS, CMMC, and SOX. These regulations mandate organizations to conduct vulnerability scans regularly to maintain the security of their systems and protect sensitive data.
|
Related reading: What Security Services Are Necessary to Be Compliant with CMMC 2.0? |
The primary purpose of vulnerability scanning is to identify and remediate vulnerabilities. Through comprehensive scanning, businesses can pinpoint vulnerabilities in their systems, applications, and network infrastructure that hackers may exploit.
There are many reasons why vulnerability scanning is essential for IT security compliance. Let's take a look at a few.
To meet regulatory requirements
Many industry regulations, such as the Payment Card Industry Data Security Standard (PCI DSS), the Cybersecurity Maturity Model Certification (CMMC), and the Sarbanes-Oxley Act (SOX), require organizations to conduct vulnerability scans on a regular basis. Not adhering to these requirements can result in fines, loss of reputation, and even loss of contracts for certain compliances. SOC 2 is another security standard that can be met by conducting external vulnerability scans. SOC 2 is a set of controls that organizations can implement to demonstrate that they have adequate security measures in place to protect sensitive data. One of the requirements of SOC 2 is to have a vulnerability management program in place. This program should include regular vulnerability scans, as well as a process for remediating any vulnerabilities that are found.
Standard (PCI DSS), the Cybersecurity Maturity Model Certification (CMMC), and the Sarbanes-Oxley Act (SOX), require organizations to conduct vulnerability scans on a regular basis. Not adhering to these requirements can result in fines, loss of reputation, and even loss of contracts for certain compliances. SOC 2 is another security standard that can be met by conducting external vulnerability scans. SOC 2 is a set of controls that organizations can implement to demonstrate that they have adequate security measures in place to protect sensitive data. One of the requirements of SOC 2 is to have a vulnerability management program in place. This program should include regular vulnerability scans, as well as a process for remediating any vulnerabilities that are found.
To identify and remediate vulnerabilities
Vulnerability scanning plays a crucial role in safeguarding organizations against potential security breaches by identifying vulnerabilities in their systems and applications that may be exploited by attackers. By promptly addressing these vulnerabilities, businesses can significantly minimize their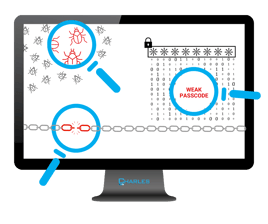 risk of a data breach.
risk of a data breach.
To demonstrate due diligence
By conducting vulnerability scanning, organizations can showcase their commitment to safeguarding their systems and data, thereby avoiding potential financial repercussions in the form of fines and penalties. This is important for any regulatory body to see, as well as building rapport with your customers.
To improve security posture
In addition to meeting compliance requirements, vulnerability scanning plays a crucial role in enhancing the overall security posture of organizations. By actively identifying and addressing vulnerabilities, businesses can effectively safeguard their data and systems against a wide range of potential threats.
Adding to the benefits listed above, external vulnerability scans can also help businesses achieve compliance with a variety of security standards. For example, PCI DSS requires merchants to conduct external vulnerability scans on a regular basis. CMMC also requires organizations that handle classified information to conduct external vulnerability scans.
|
Related reading: IT Budgeting Best Practices: Include A Vulnerability Scanning Program |
Here are some of the things to consider when conducting external vulnerability scans:
vulnerability scans:
- Use a reputable vulnerability scanning vendor. There are many different vulnerability scanning vendors on the market. It is important to choose a vendor that has a good reputation and that offers a comprehensive vulnerability scanning solution.
- Scan all public-facing assets. External vulnerability scans should scan all public-facing assets, including websites, web applications, and network devices.
- Scan on a regular basis. The frequency of external vulnerability scans will vary depending on the organization's risk profile. However, it is generally recommended to scan on a monthly or quarterly basis.
- Remediate any vulnerabilities that are found promptly. Once vulnerabilities are found, they should be remediated promptly. This will help to reduce the risk of a data breach.
Vulnerability scanning is an essential part of any organization's IT security compliance program. By conducting regular vulnerability scans, businesses can help protect their data and achieve compliance with a variety of security standards. This can help them avoid costly fines and penalties, and it can also help them build trust with their customers and partners.
Expert guidance and reliable IT services from Charles IT now can help make future compliance easier. Contact us today to get started!




