If your company has contracts with the Department of Defense or any other federal agency, you'll need to pay close attention to DFARS regulations. These rules are crucial for ensuring compliance and avoiding penalties. Failure to abide by DFARS can have serious repercussions, including the possibility of stopping your business operations altogether.
As anticipated, operating as a defense contractor for the federal government entails additional obligations that aren't required in the private sector. One heightened area is the demand for cybersecurity measures to combat increasingly sophisticated cyber threats.
The Defense Federal Acquisition Regulation Supplement (DFARS) is a set of regulations aimed at prioritizing the security of organizations and their customers.
First, let’s look at what DFARS encompasses and then consider how a contractor can achieve compliance.
What is DFARS?
DFARS was published by the Department of Defense (DoD) in 2015. The primary purpose of DFARS is to protect the confidentiality of Controlled Unclassified Information (CUI)— and regulations apply to all DoD contractors.
The DFARS assessment is also part of the CMMC 2.0 Level 2 certification, which is a third-party
certification system. Although CMMC 2.0 Level 1 allows for self-certification, a DFARS self-certification won't get you to level two. CMMC 2.0 certification is required for contractors to bid on all requests, and, if you're handling CUI, you're going to need at least a third-party assessor to complete your DFARS certification.What is CUI?
Before considering the ramifications of a DFARS compliance audit, it’s essential to note what exactly constitutes CUI. In short, CUI is simply information that is sensitive and in the interests of the United States but is not strictly regulated by the Federal government.
CUI includes any potentially sensitive and unclassified information needing controls to be in place that define methods for safeguarding or dissemination. Each federal agency has provided a public registry of categories and subcategories of CUI and determines why information is considered CUI.
Who Needs to Be DFARS-Compliant?
Anyone doing contract work for the DoD and other federal agencies is required to be DFARS-compliant. Whether you belong to one of the larger defense contractors or a smaller organization, becoming DFARS-compliant is a must. Even if you don't currently engage in any work for the DoD, you can take advantage of future opportunities by becoming DFARS-compliant.
What Is NIST 800-171?
Yes -- there's another layer here! We know it's a lot, but we've got you.
The National Institute of Standards and Technology Special Publication 800-171 (NIST 800-171) is a collection of regulations that govern CUI in Non-Federal Information Systems and Organizations. NIST 800-171 establishes a set of standards that apply to safeguarding and distributing data that is considered sensitive but not classified.
NIST 800-171 seeks to enhance cybersecurity and was established following several well-documented breaches in various federal agencies.
A revised version of NIST compliances was introduced in 2017, which requires anyone working with CUI as part of the DoD, General Services Administration (GSA), or National Aeronautics and Space Administration (NASA) to adopt security measures in handling data. NIST 800-171 was updated again in 2024 to provide federal agencies with recommended security requirements for protecting the confidentiality of CUI when the information is residing in nonfederal systems and organizations where there are no requirements.
Federal regulations, including the DFARS clause 252.204-7012, require that all companies that handle CUI must assess and document their compliance in many critical areas.
14 Key Points of NIST 800-171

All contractors that deal with CUI are required to pass a DFARS compliance audit and introduce security protocols in 14 critical areas. These areas include:
- Audit and Accountability
- Awareness and Training
- Access Controls
- Incident Response
- Identification and Authentication
- Configuration Management
- Media Protection
- Maintenance
- Personnel Security
- Physical Protection
- Security Assessment
- Risk Assessment
- System and Information Integrity
- System and Communications Protection
To comply with NIST 800-171, any contractor that stores, transmits, or processes CUI for the GSA, NASA, DoD, or any other state or federal agency must meet a number of strict standards. This process requires all contractors to assess networks and procedures to ensure adequate security measures are in place. The failure to achieve NIST 800-171 compliance could result in the severance of contracts and severely damage work relationships with federal agencies.
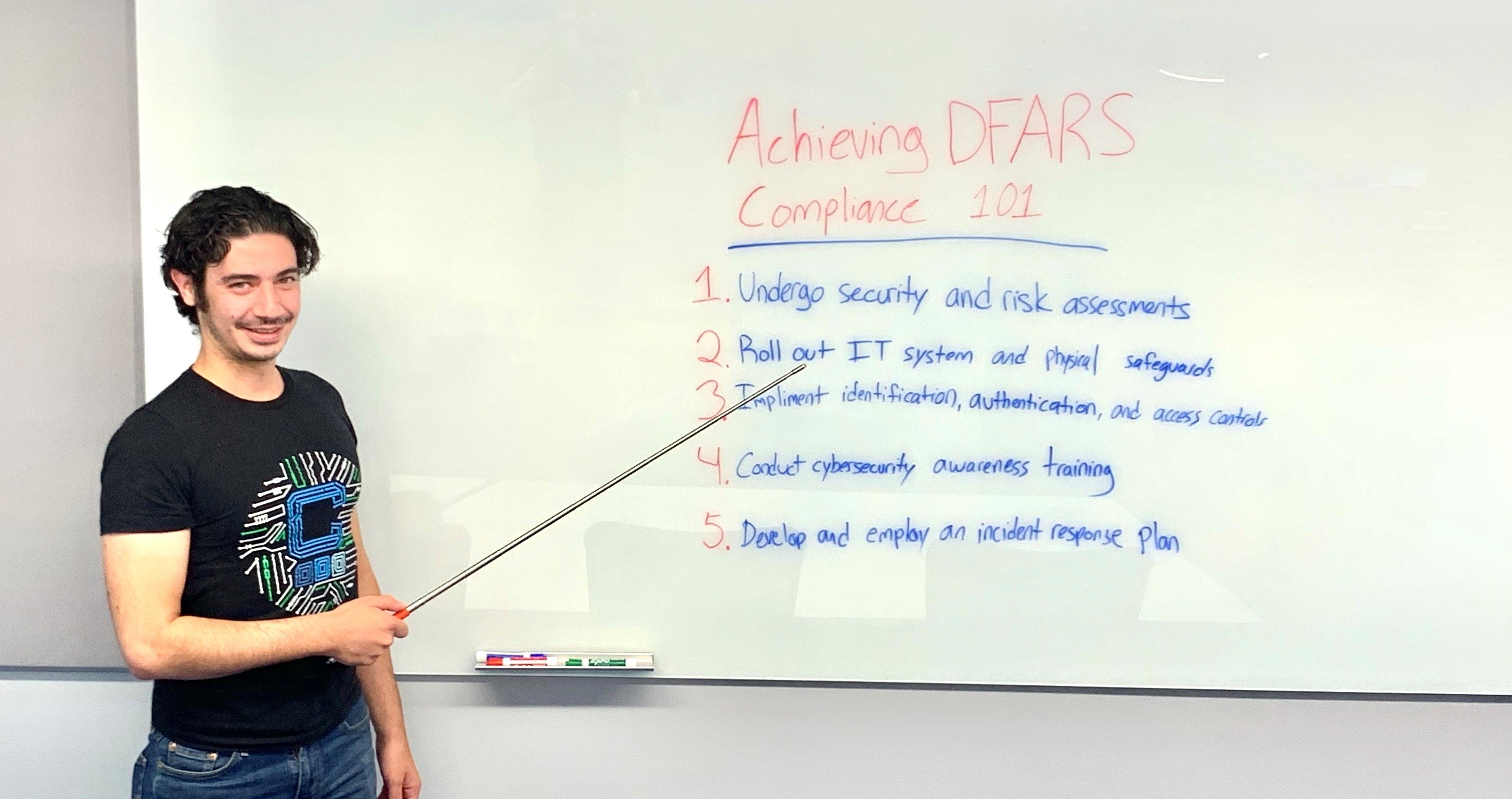
What Are the Basic Conditions to Comply with DFARS?
There are several basic requirements in meeting a DFARS compliance audit. These include:
- Adopting 79 fundamental security protocols
- Providing effective intrusion monitoring as well as disclosing incidents
- Introducing cyber incident reporting and analysis
- Ensuring the proper handling of all information relating to OpSec Information, Export-Controlled Information, and Controlled Technical Information, as well as all other data related to contracts regardless of the location
What Are Some of the Challenges in Becoming Compliant?
The process of compliance must begin with a comprehensive security assessment. It's important to identify the location of sensitive information and create a compliance team to monitor CUI while including all staff members in all processes. Though there are no guidelines outlined for the DFARS assessment, you should plan on running a security assessment two or more times per year, and run an additional security assessment whenever your company implements a change to relevant operations.
You must also restrict access controls as subject to the standards expressed in NIST SP800-171. Given the extensive nature of cloud-based systems and that most breaches are initiated by stolen login credentials, this is a crucial step in becoming DFARS-compliant. The principle of least privilege can help mitigate any risks and foster compliance, as having employees only access data required for their jobs will limit potential difficulties.
Staff training and awareness are also critical elements to ensure DFARS compliance. Data leaks and breaches most often occur due to human error. Social engineering attacks such as phishing further highlight the need to make sure your staff is aware of risks and capable of mitigating these risks.
For further guidance on DFARS compliance resources, feel free to explore our free eBook! Simply click here to download your copy.
Becoming Compliant Takes Time
It can take months to become fully compliant. The first step is to understand what DFARS is and conduct a DFARS assessment. It is crucial that you learn the list of regulations that apply to contractors working with federal agencies, or have someone on your team that knows them inside and out. In the end, becoming compliant not only meets the legal requirements of being a DoD contractor but also provides your partners assurance in knowing that their information is adequately protected and managed.
You have help available in complying with DFARS and NIST 800-171. An MSP like Charles IT knows precisely how organizations can best comply with their standards. Our experts can help you achieve the additional security needed for DFARS compliance while saving you costly investments in the process. Drop us a line today to get started on your path to compliance!
Editor's Note: This post was originally published in July 2020 and has been updated for accuracy and comprehensiveness.

.png)