If you manage a business, you already know that there are many ways your business can be exposed to cyber threats. This is why businesses must conduct a variety of security measures to remain secure, including network risk assessments. While there are numerous cybersecurity strategies that business owners can follow to avoid a cybersecurity incident, the best place to start is by knowing your current risk level.
Ask yourself, "What risk level would a rate my business at right now?
- Zero-risk
- Low-risk
- Medium-risk
- High-risk
Now ask yourself, "How certain am I that I'm correct in my assumption?"
Knowing concretely where your company stands, based on a cybersecurity risk assessment, is crucial. It will help you determine what security measures to implement or whether your existing measures are adequate. As a bonus, it will also help you budget both time and resources for your IT environment well into the future.
What Is a Cybersecurity Risk Assessment?
A cybersecurity risk assessment helps identify, analyze, and evaluate risks unique to a company. According to the National Institute of Standards and Technology, a cybersecurity risk assessment must involve examining specific risks to IT assets, operations, people, and the entire organization for every operational step that uses data systems.
A good risk assessment should address important security concerns such as:
- Identifying your most valuable assets
- Knowing the impact data breaches have on your company and your customers’ data
- Identifying specific threats targeting your industry
In certain industries, cybersecurity risk assessments are required by regulatory authorities, such as the General Data Protection Regulation, HIPAA, and Sarbanes-Oxley, which all lay baselines of security standards to ensure that all organizations are adequately protected.
How Does a Cybersecurity Risk Assessment Help with SOC 2 Compliance?
Does your business use the cloud to store customer data? If so, you MUST complete a cybersecurity risk assessment to be SOC 2 compliant.
Any organization that uses the cloud to store customer data must comply with the Systems and Organizations Controls version 2 (SOC 2), a crucial component of the American Institute of CPAs’ Service Organization Control reporting platform. Although not mandatory, obtaining SOC 2 certification provides many important benefits.
SOC 2 requires organizations to create solid and clearly outlined security policies covering the following components:
- Security,
- Availability,
- Processing Integrity,
- Confidentiality,
- and Cloud Data Privacy.
This entails monitoring systems for suspicious activity, including unauthorized access, phishing attempts, and zero-day threats. Your organization must be able to distinguish between a normal activity and an abnormal one on your cloud infrastructure. This can be done by implementing a network security assessment, among other similar measures.
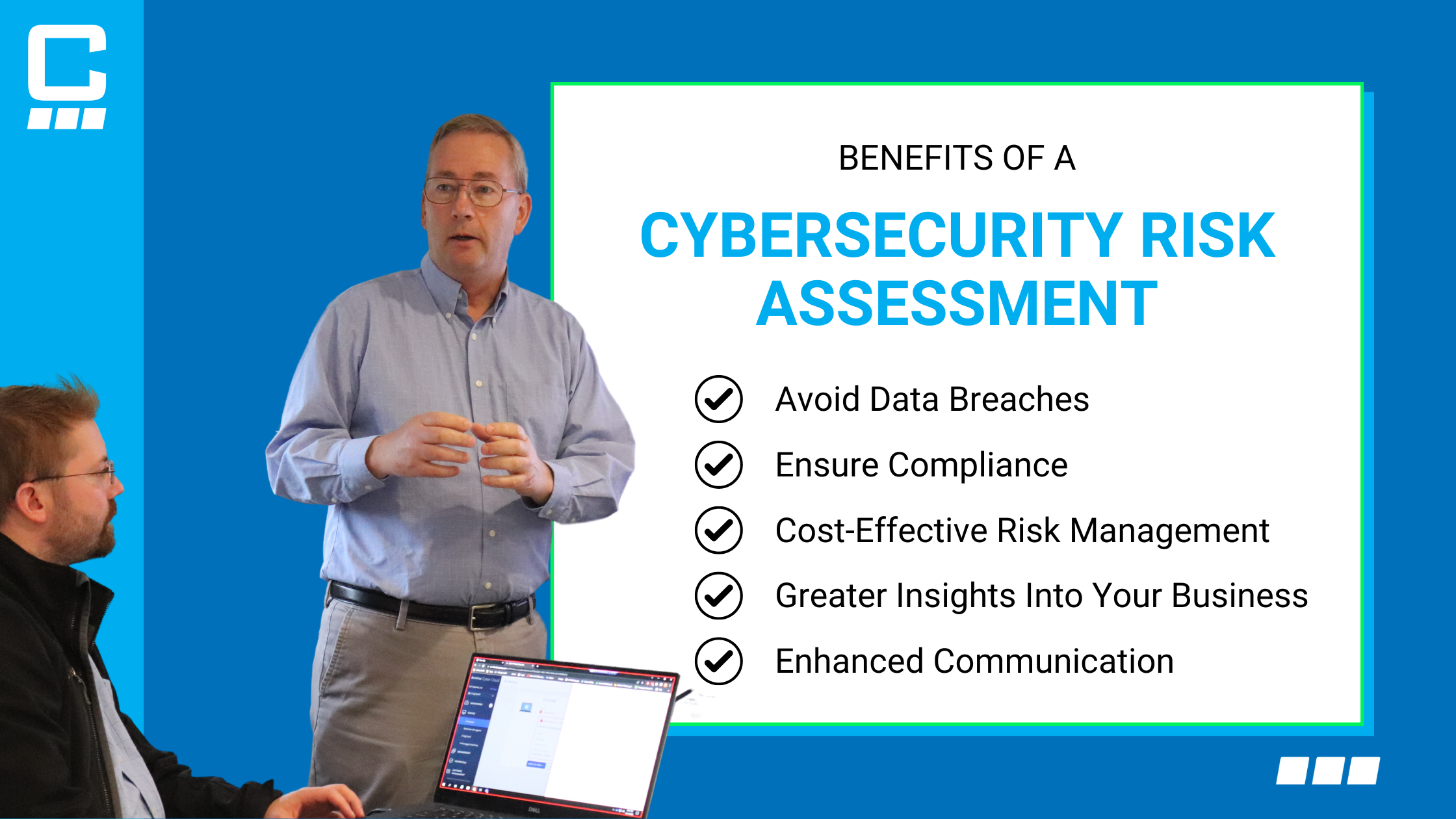
Other ways that a risk assessment focused on network security can help your business include:
- Avoiding Data Breaches – The main reason to conduct a cyber risk assessment is to avoid data breaches. Knowing the risks unique to your organization is key to preventing them.
- Ensure Compliance – It’s a practical first step to ensure compliance with various regulations. Regularly conducting a risk assessment keeps your organization one step ahead of any changes in compliance rules, making it easier for you to comply even when those rules evolve.
- Cost-Effective Risk Management – A SOC 2 audit has its own associated costs. A best-guess estimate for these would start at $20,000 and could go higher, depending on factors such as the scope of the report and the size and nature of the business. Still, these costs are a lot less than the cost of mitigating a data breach, which can be in the millions of dollars. The foresight that a risk assessment provides significantly reduces, if not eliminates, the likelihood of succumbing to threats and consequently failing to comply with SOC 2 and other kinds of audits.
|
Related reading: SOC 2 Explained: SOC 2 Type 1 Vs. Type 2 Compliance |
- Greater Insights Into Your Business – Conducting a risk assessment gives you deep insights into your business, including your security position and your overall level of preparedness for threats. This will then help you assess your readiness for a SOC 2 audit and benefit you by providing greater insight into your operations and growth prospects.
- Enhanced Communication – Complying with SOC 2 requires different business departments and stakeholders to combine efforts. The IT teams or outsourced IT experts handling SOC 2 compliance must communicate every aspect of the process to business decision-makers who will then be tasked with communicating its importance to the entire organization. A cybersecurity risk assessment improves business communications across all levels. Every staff member and business executive must know how to practice good cybersecurity habits, whom to report to in the event of one, and how to respond to any possible cyberattack.
We can all agree that a cybersecurity risk assessment is vital to SOC 2 compliance. Equipped with the knowledge of your business's exact level of risk, you can build upon this and benefit from continuous monitoring services, which mitigate most IT issues through regular maintenance and constant vigilance.
Let the experts at Charles IT conduct your security assessments. We’ll ensure all bases of your SOC 2 compliance are covered. Get in touch with our team by calling us or leaving a message.
Editor's Note: This post was originally published in February 2021 and has been updated for accuracy and comprehensiveness.

.png)